Firewall or Fine 1990s Cyberlaw Quiz





Quiz Complete!
Firewall or Fine: How the 1990s Invented the Rules of the Internet
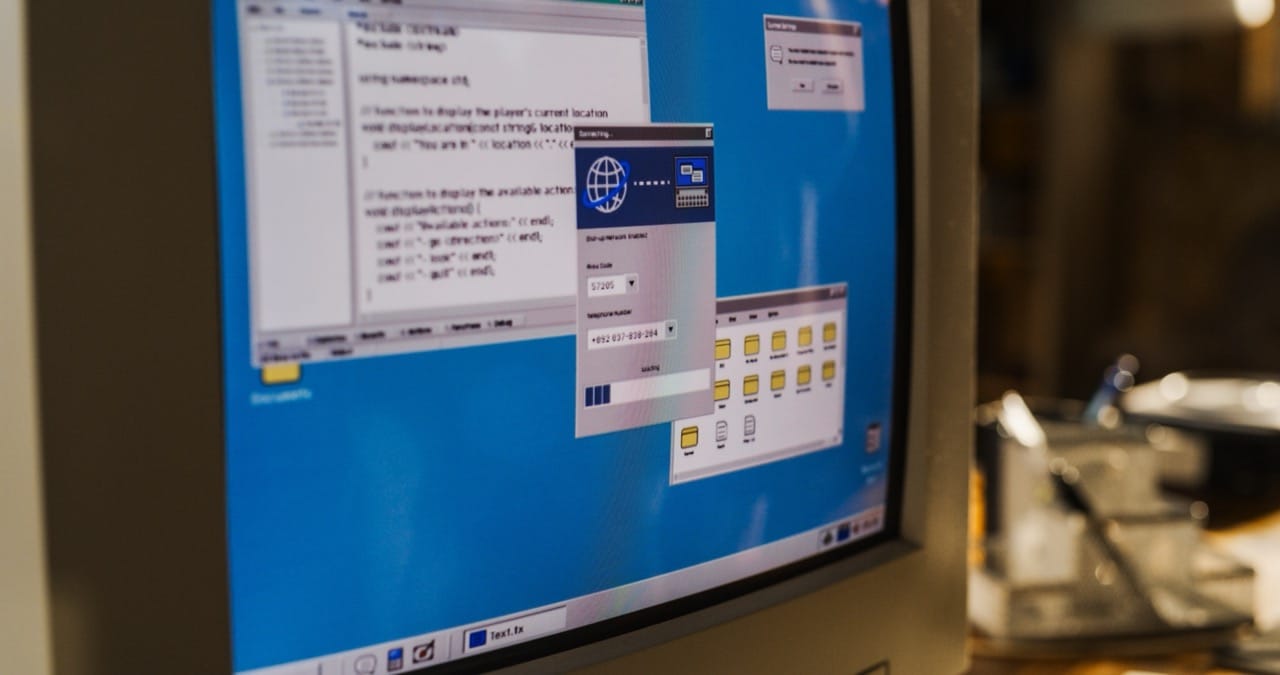
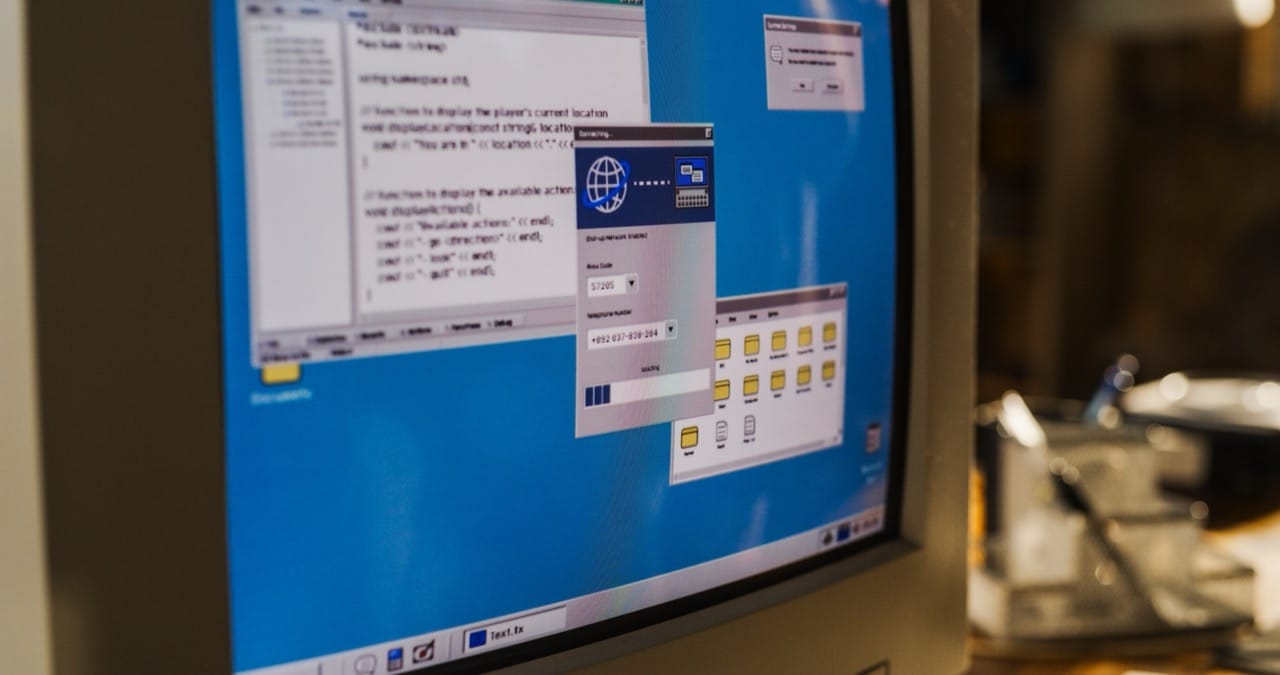
In the 1990s, the internet stopped being a hobby for universities and tech enthusiasts and became something ordinary people used at home, often through noisy dial up modems and early web browsers. That sudden shift forced governments and courts to answer questions that sounded simple but were legally strange at the time. What counts as breaking in when you never touch a physical lock. Is an email private like a sealed letter, or more like a postcard passing through many hands. If a song becomes a file, is copying it the same as stealing a CD.
One of the decade’s most important U.S. laws was the Computer Fraud and Abuse Act, originally passed in the 1980s but expanded and relied on heavily in the 1990s as networked computing spread. It aimed to punish unauthorized access to computers, but the meaning of unauthorized became a lasting puzzle. Early cases and later controversies grew from the same basic tension: the law wanted to stop real intrusions and damage, yet networks were built for sharing, and people often wandered into places they technically could reach. The 1990s also saw high profile attention on hacking culture, with incidents that helped push lawmakers to treat digital break ins as serious crimes rather than pranks.
Privacy law had to adapt too. The Electronic Communications Privacy Act of 1986 was the key federal framework, but the 1990s revealed its limits. It tried to extend wiretap style protections to electronic communications and to stored messages, yet it was written before webmail, social media, and cloud storage. In practice, a major question was when the government needed a warrant and when it could use lesser legal tools to obtain emails or subscriber records. Another major development was the Communications Assistance for Law Enforcement Act of 1994, which required telecommunications carriers to design systems that could support lawful interception. Even then, the line between traditional phone networks and the internet was already blurring, setting up arguments that still echo today.
Few topics capture the decade’s mood better than the encryption battles. Strong encryption was becoming accessible to ordinary users, promising privacy and security in a world where online banking and shopping were just emerging. But the U.S. government worried that widespread encryption would hinder investigations. Export controls treated strong cryptography like a weapons technology, limiting what companies could ship overseas. The Clipper Chip proposal, with a government held key escrow system, became a symbol of the era’s struggle to balance security, privacy, and state power. Public backlash and technical criticism helped sink the idea, and by the end of the decade restrictions began to loosen, paving the way for the encrypted web people now take for granted.
Speech online created its own legal emergency. The Communications Decency Act of 1996 attempted to restrict indecent material online, but the Supreme Court struck down major provisions in Reno v. ACLU, recognizing the internet as a uniquely broad platform for expression. In the same law, a different section became hugely influential: Section 230, which largely protects online services from being treated as the publisher of user posts while allowing them to moderate. That legal shield helped forums, early community sites, and later social platforms scale up without being crushed by liability for everything users might say.
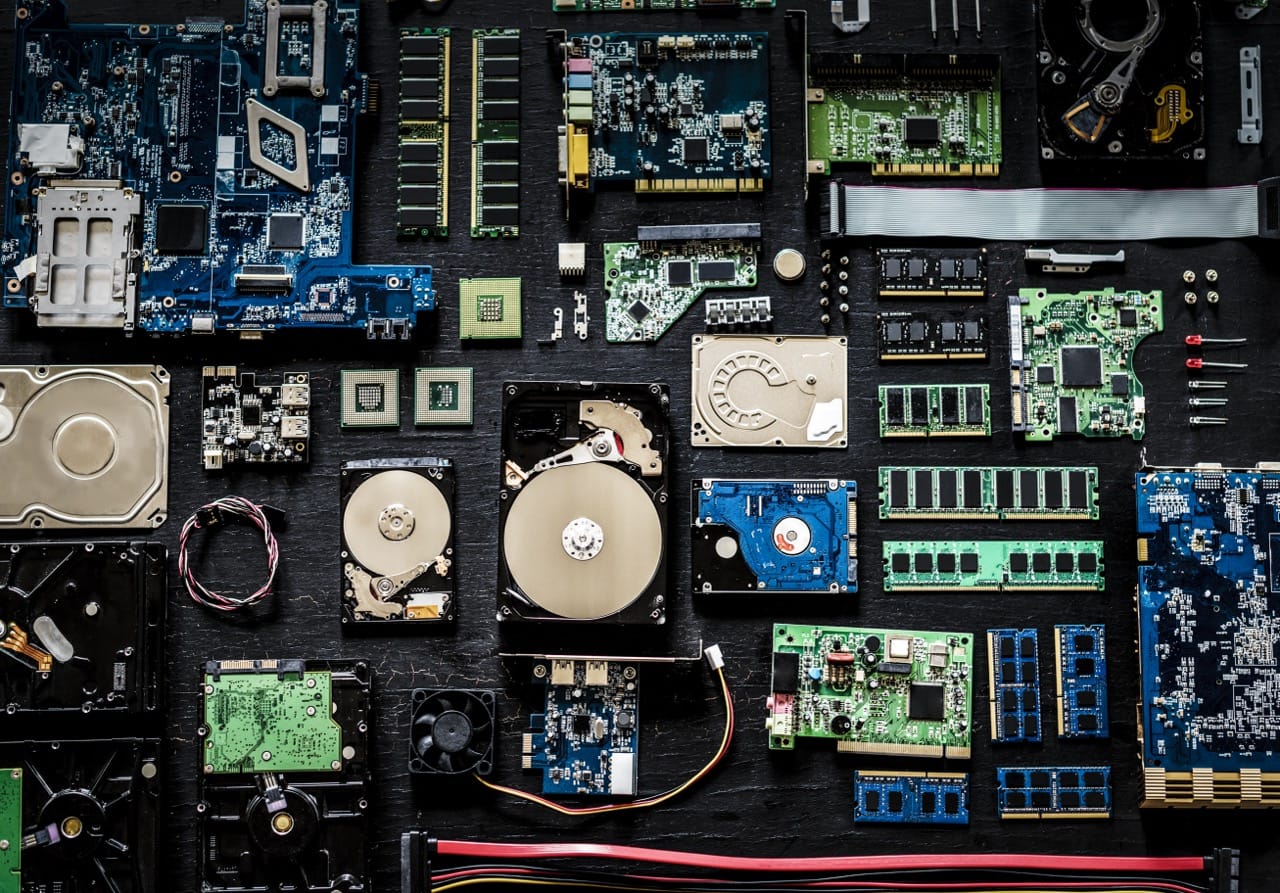
Copyright law faced a shock when perfect digital copies became easy. The Audio Home Recording Act of 1992 tackled consumer digital recording devices and included a levy system, but it did not anticipate MP3s and peer to peer sharing. As copying moved online, lawmakers passed the Digital Millennium Copyright Act in 1998. The DMCA created notice and takedown rules that protect online platforms if they remove infringing material when notified, and it also banned circumvention of digital locks. Those anti circumvention rules became controversial because they can affect legitimate activities like security research, repair, and archiving, even when no piracy is involved.
The 1990s were also international. The EU Data Protection Directive of 1995 set a strong baseline for personal data handling and cross border transfers, influencing later global privacy norms. Meanwhile, negotiations at the World Intellectual Property Organization produced treaties in 1996 that pushed countries toward stronger protections for digital works, feeding into laws like the DMCA.
What makes 1990s cyberlaw so fascinating is how many of its arguments feel familiar. Courts and lawmakers were trying to map old concepts onto new technology, sometimes getting it right, sometimes creating awkward rules that lasted anyway. The decade’s legal experiments built the foundation for today’s debates about hacking, privacy, platform responsibility, and digital ownership, all born in the era of dial up, chat rooms, and the first time society realized the internet was not a toy but a place where real life happens.